In today's digital age, remote access has become an essential tool for businesses and individuals alike. VNC behind firewall technology allows users to securely connect to remote computers even when they are protected by a firewall. This guide will explore everything you need to know about VNC behind firewall, including its benefits, challenges, and solutions.
As more people work remotely, the demand for secure and efficient remote access solutions has grown significantly. VNC (Virtual Network Computing) is one of the most popular tools for remote desktop access, enabling users to control another computer over the internet as if they were sitting in front of it. However, firewalls can sometimes pose challenges to establishing these connections.
This article will provide a detailed overview of VNC behind firewall, including practical tips and strategies to overcome common obstacles. Whether you're a network administrator, IT professional, or simply someone looking to enhance your remote working capabilities, this guide will equip you with the knowledge you need to succeed.
Read also:Kylie Jenners Dad The Story Behind The Fame
Table of Contents
- Introduction to VNC
- Understanding Firewalls
- VNC Behind Firewall Challenges
- Solutions for VNC Behind Firewall
- Best Practices for Secure Connections
- Common Mistakes to Avoid
- Tools and Software Options
- Case Studies
- Future Trends
- Conclusion
Introduction to VNC
VNC, or Virtual Network Computing, is a graphical desktop sharing system that allows users to remotely control another computer. It transmits the keyboard and mouse events from one computer to another, relaying the screen updates back in the opposite direction, over a network. VNC has become an indispensable tool for remote work, IT support, and system administration.
How VNC Works
VNC operates on a client-server model. The server is installed on the computer you want to control remotely, while the client is installed on the machine from which you want to control it. When a connection is established, the client receives screen updates from the server and sends keyboard and mouse inputs back to it. This process happens in real-time, enabling seamless interaction with the remote computer.
Popular Use Cases
- Remote work and telecommuting
- IT support and troubleshooting
- System administration and monitoring
- Collaboration and team management
Understanding Firewalls
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Firewalls act as a barrier between trusted internal networks and untrusted external networks, such as the internet. They help protect computers and networks from unauthorized access and cyber threats.
Read also:Top Hotels Near Northbrook Court Mall Your Ultimate Guide
Types of Firewalls
- Packet-filtering firewalls
- Stateful inspection firewalls
- Application-layer firewalls
- Next-generation firewalls
Firewalls play a critical role in maintaining network security. However, they can sometimes block legitimate traffic, including VNC connections, which can pose challenges for remote access.
VNC Behind Firewall Challenges
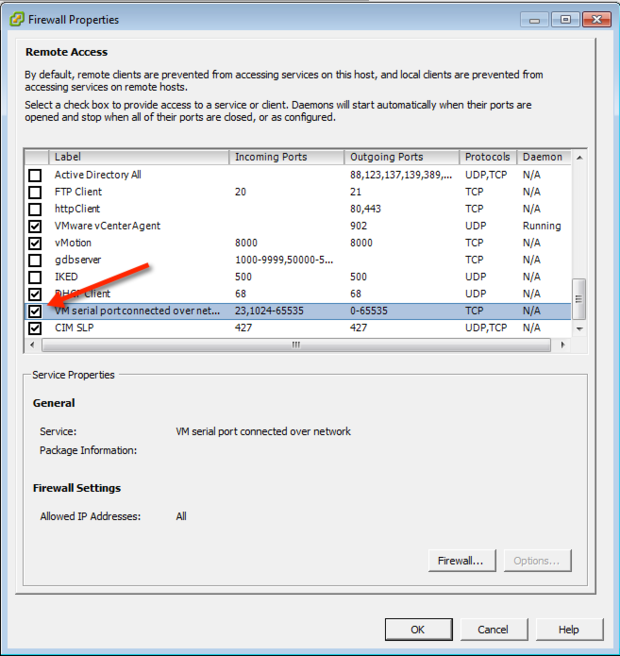
One of the most common challenges when using VNC is establishing a connection when the remote computer is behind a firewall. Firewalls are designed to block unauthorized access, and they often restrict incoming connections on specific ports, including those used by VNC.
Common Issues
- Blocked ports: Firewalls may block the default VNC port (5900) or any custom ports configured for VNC.
- Network address translation (NAT): NAT can make it difficult to establish direct connections between devices on different networks.
- Security policies: Strict security policies may prevent VNC connections from being established.
Overcoming these challenges requires a combination of technical knowledge and strategic planning.
Solutions for VNC Behind Firewall
There are several solutions available for establishing VNC connections behind a firewall. These solutions range from simple configuration changes to more advanced techniques involving third-party tools and services.
Port Forwarding
Port forwarding involves configuring your router to forward incoming traffic on a specific port to the internal IP address of the VNC server. This allows you to establish a direct connection to the remote computer, even when it is behind a firewall.
Using a Proxy Server
A proxy server acts as an intermediary between the VNC client and server, enabling connections to be established through firewalls. Proxy servers can also enhance security by encrypting traffic and hiding the internal IP address of the VNC server.
Utilizing Cloud-Based Solutions
Cloud-based VNC solutions, such as TeamViewer or AnyDesk, provide an easy way to establish remote connections without the need for port forwarding or proxy servers. These services use secure tunnels to bypass firewalls and enable seamless remote access.
Best Practices for Secure Connections
When using VNC behind a firewall, it's essential to follow best practices to ensure secure connections. This includes implementing strong authentication, encrypting traffic, and regularly updating software.
Strong Authentication
Use strong passwords or multi-factor authentication (MFA) to protect VNC connections from unauthorized access. Avoid using default passwords and ensure that all users have unique credentials.
Encrypting Traffic
Enable encryption for all VNC connections to protect sensitive data from interception. Most VNC clients and servers support encryption protocols such as TLS or SSL, which can be enabled through configuration settings.
Regular Updates
Keep your VNC software up to date with the latest security patches and bug fixes. Regular updates help protect against known vulnerabilities and ensure optimal performance.
Common Mistakes to Avoid
While VNC behind firewall can be a powerful tool, there are several common mistakes that users should avoid to ensure successful and secure connections.
Ignoring Security
One of the biggest mistakes is neglecting security measures, such as using weak passwords or failing to encrypt traffic. This can leave your network vulnerable to cyberattacks and unauthorized access.
Improper Configuration
Misconfiguring your firewall or VNC settings can prevent connections from being established. Always double-check your settings and consult the documentation if necessary.
Overlooking Updates
Failing to update your VNC software can expose your network to known vulnerabilities. Regularly check for updates and apply them promptly to ensure maximum security.
Tools and Software Options
There are several tools and software options available for VNC behind firewall, each with its own strengths and weaknesses. Choosing the right tool depends on your specific needs and requirements.
Open Source Solutions
- TightVNC
- RealVNC
- UltraVNC
Commercial Solutions
- TeamViewer
- AnyDesk
- LogMeIn
Each of these tools offers unique features and capabilities, so it's important to evaluate them carefully before making a decision.
Case Studies
Real-world examples can provide valuable insights into how VNC behind firewall solutions are implemented in practice. Below are two case studies illustrating successful implementations of VNC technology.
Case Study 1: Small Business
A small business used VNC to enable remote access for its employees. By configuring port forwarding and implementing strong authentication, they were able to establish secure connections without compromising network security.
Case Study 2: Enterprise Organization
An enterprise organization implemented a cloud-based VNC solution to support its global workforce. This solution enabled seamless remote access while maintaining strict security standards and compliance with regulatory requirements.
Future Trends
The future of VNC behind firewall is likely to be shaped by advancements in technology and evolving security threats. Some key trends to watch include:
- Increased adoption of cloud-based solutions
- Enhanced security features, such as AI-driven threat detection
- Integration with other remote access technologies
Staying informed about these trends will help you make better decisions when implementing VNC behind firewall solutions.
Conclusion
VNC behind firewall is a powerful tool for remote access, enabling users to connect to remote computers securely and efficiently. By understanding the challenges and solutions associated with VNC behind firewall, you can overcome common obstacles and ensure successful connections.
We encourage you to explore the tools and software options discussed in this guide and implement best practices to enhance security. If you found this article helpful, please share it with others and leave a comment below. For more information on remote access and network security, check out our other articles on the site.